In the vast landscape of the music business, Spotify stands out as a leading platform for artists to showcase their…
Paramount Error 3002 is a common issue encountered by users when attempting to access content on the Paramount+ streaming platform.…
Protecting digital assets from ever-evolving cyber hazards is a difficult task for enterprises in a time when cyber threats are…
A VPN diverts a device’s internet connection through a private service, concealing the user’s IP address and creating an encrypted…
Many people are attracted to trading in the financial markets as a way to potentially earn income. However, most beginners…
To understand what cold storage is, it’s necessary to first learn the principles of the “bitcoin wallet.” In the same…
Are you a business owner? Do you want to improve your business online? If you do, you need to understand…
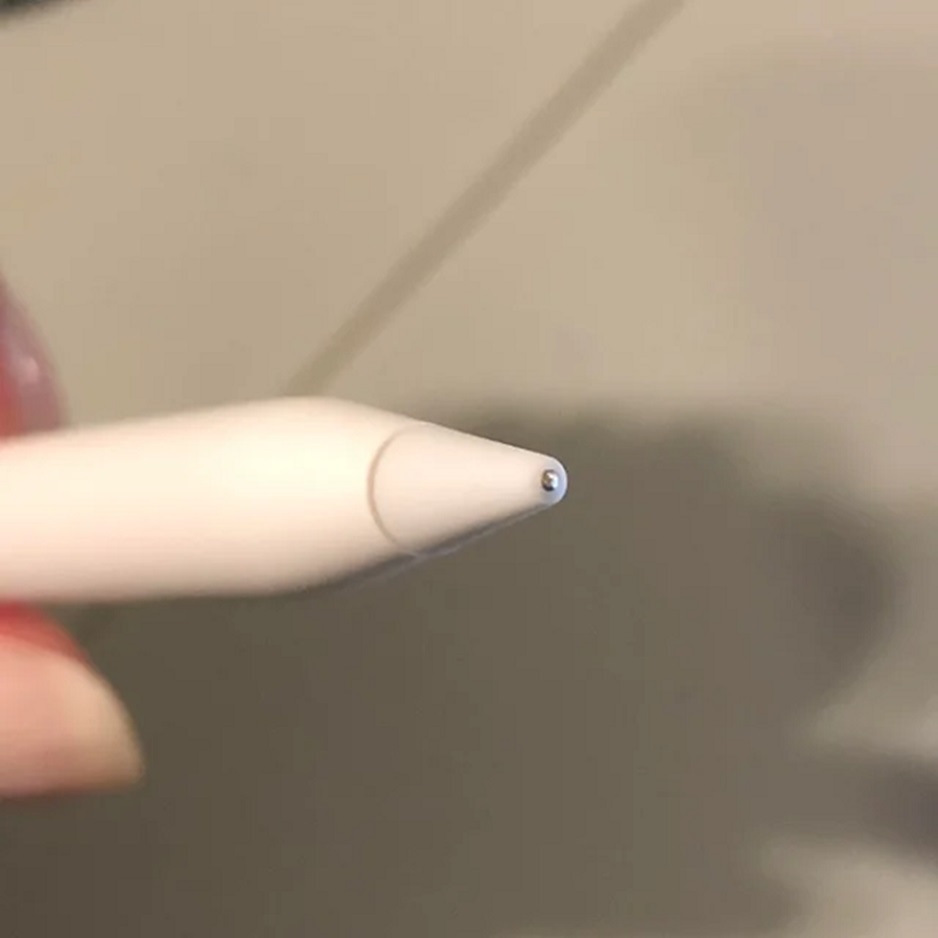
Apple Pencil may feel even more fluid than a traditional pen upon first use. Yet, it doesn’t live forever, just…
Inventory management is a critical aspect of running a successful restaurant. Wastage, overstocking, or understocking can all have a significant…
A virtual data room (VDR) can be useful for a variety of teams who need secure collaboration and sharing. Tasks…